Recently I got a 8 year old Dell notebook with i3 CPU with one small issue - a blown diode preventing it from powering on. Because this computer must have an up to date BIOS not to overheat in Linux (yes, this thing in which video chip controls overall cooling), I found Dell website deleted it, leaving only revision 12, which is OK for corporate users, but revision 13 makes the system overheat less.
I finally got my rev. 13 BIOS and flashed it, so the computer does not overheat. I got it from some random computer shop website in a distant place in Russia (Omskaya Oblast) - all other links were dead.
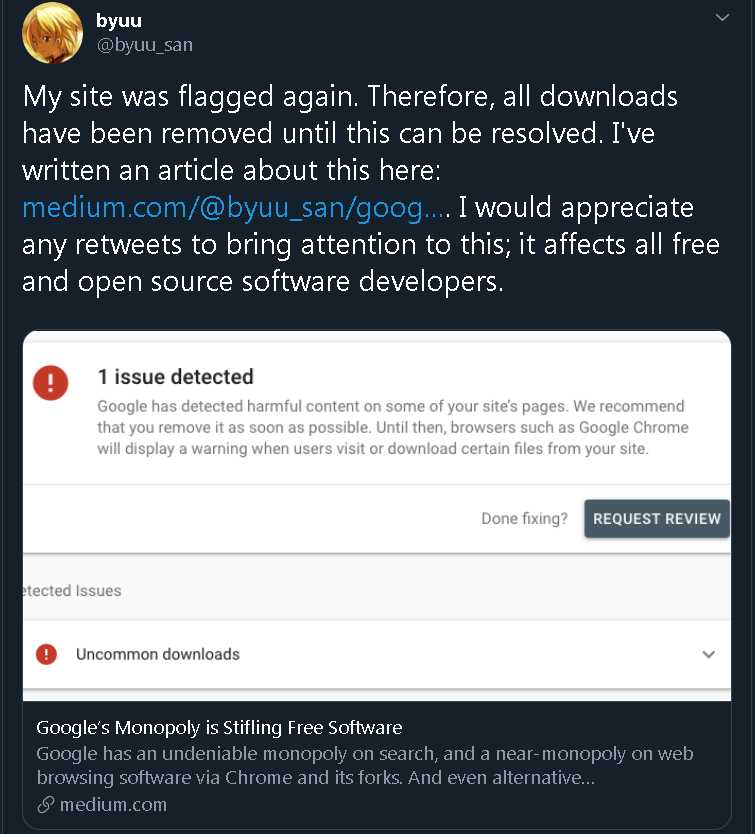
We may f..k Google as much as we can, but this does not mean that Google will not f..k the Internet and make useful things disappear even faster.
And one more thing: Some time ago I wrote a simple program which does the following:
1. Ensures Win9x are run, not NT, not XP. Only 95 or 98, if not puts a help message.
2. Saves current year and cranks the system clock it to 2013.
3. Launches a processes form a hard-coded file if exists, if not puts a help message.
4. Clocks the year back.
The only goal of this software was removal of a timebomb in a diagnostic program which could blow up when started in 2014. In fact, even creator of this software recommends clocking the system back, as he lost the source code. I built it in Pascal and C++ to compare which will be smaller. I found Pascal version larger at first, but easier to compress in transit, but that's another story.
Let's submit to VirusTotal: About 20% of AV informed me that it's a virus. Generally names containing "GEN".
I tried building sources on other computers because I could be infected - but no! Antivirus software just detects it as some virus. Today it's just impossible to get any information about meaning of a specific virus - it's bad because it's bad. Do not ask. By trial and error I found that the thing which makes the file a "virus" is a sequence: Setting the clock back, then running process.
You can have other opinions, but I think that someone just bought this detection in antivirus software to prevent "trial resetting" applications.
And is this the great oracle which states what file can and what cannot be downloaded? Which is just a commercial fraud?